For anybody with substantial bitcoin holdings, a custody construction that features a single level of failure must be seen as unacceptable. If a pockets has a single element that—when misplaced or stolen—can result in a everlasting lack of funds, then it’s just too harmful to contemplate. No one needs to maintain important wealth teetering on the sting of disaster.
Particular person bitcoin holders have quite a few instruments accessible that may assist cut back the danger of loss or theft. In a earlier article, we coated a few of these instruments, highlighting modifications generally utilized to singlesig wallets. Nevertheless, we additionally defined why these approaches fall in need of eradicating single factors of failure completely.
For a enterprise, authorities, or different establishment that desires to safe a bitcoin treasury, eliminating single factors of failure isn’t just a nice-to-have, however a prerequisite. The one custody fashions price contemplating for these entities are ones that embrace a threshold requirement with a purpose to entry funds. A threshold requirement describes a construction that includes a number of, individually secured elements, the place a subset of these elements are wanted to approve any withdrawal. That is the one method of reaching institutional-grade safety, with single factors of failure eradicated fully.
On this article, we’ll cowl learn how to apply threshold safety utilizing three completely different strategies: script multisig, Shamir’s secret sharing (SSS), and multi-party computation (MPC). We’ll additionally dive into the tradeoffs related to every method, and the way an establishment can select the very best setup to satisfy their wants.
What’s multisig?
In the event you aren’t positive what script multisig is, we advocate trying out our earlier article devoted to explaining how multisig wallets work and what they’re used for. As a fast evaluate, a multisignature pockets includes a number of non-public keys, and could be configured so {that a} particular quantity (threshold) of these non-public keys are required to signal any transaction. The signatures could be produced at completely different instances and places, permitting every key to stay bodily separated. As soon as a threshold variety of signatures have been produced, they are often mixed right into a single bitcoin transaction able to spending the funds.
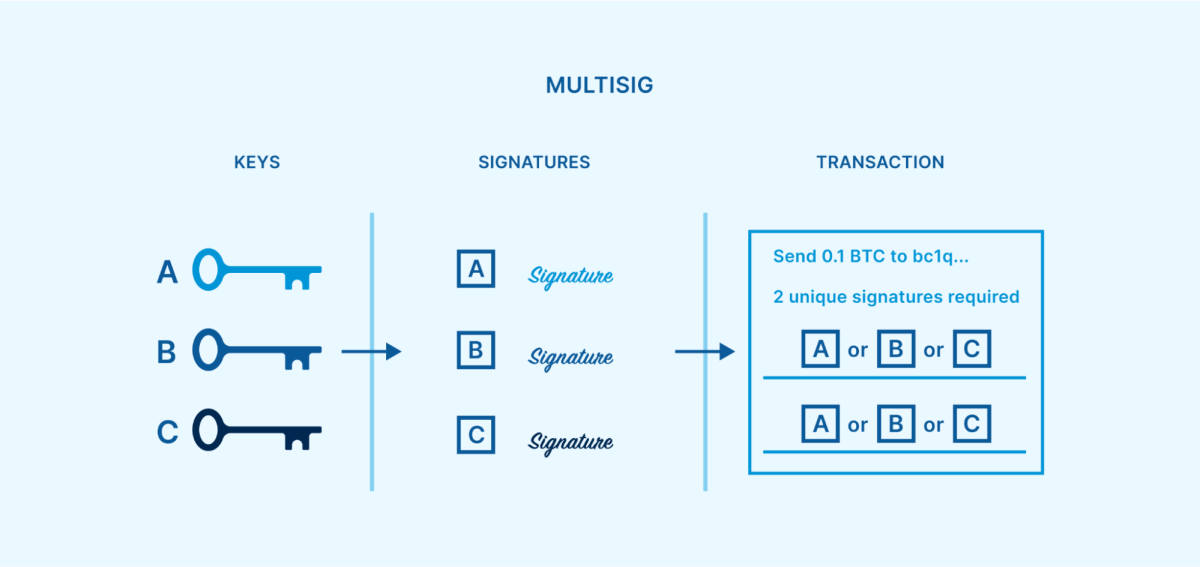
This comparatively easy method of making a threshold requirement is extremely efficient at eradicating all single factors of failure. So long as the spending threshold is bigger than one however lower than the overall variety of keys, then any single key can turn into misplaced, stolen or destroyed with out bitcoin changing into unrecoverable. The remaining keys may signal a restoration transaction shifting funds to a recent multisig setup.
Satoshi Nakamoto laid the groundwork for multisig when bitcoin was first launched, anticipating that it might be a well-liked mechanism for securing funds. Nevertheless, it wasn’t till the P2SH softfork in 2012 that multisig began to turn into a broadly used instrument. Multisig has since confirmed itself as a battle-tested safety mannequin for greater than a decade, throughout a number of completely different tackle varieties.
What’s Shamir’s secret sharing?
Shamir’s secret sharing (SSS) is a secret sharing algorithm that was developed by famend cryptographer Adi Shamir in 1979. It may be used as one other method of introducing a threshold requirement for shielding bitcoin. SSS permits customers to separate a key into a number of distributed “shares,” with solely a sure threshold of the shares wanted to reassemble the important thing. This can be utilized to design quorums like 2-of-3 or 3-of-5, much like multisig.
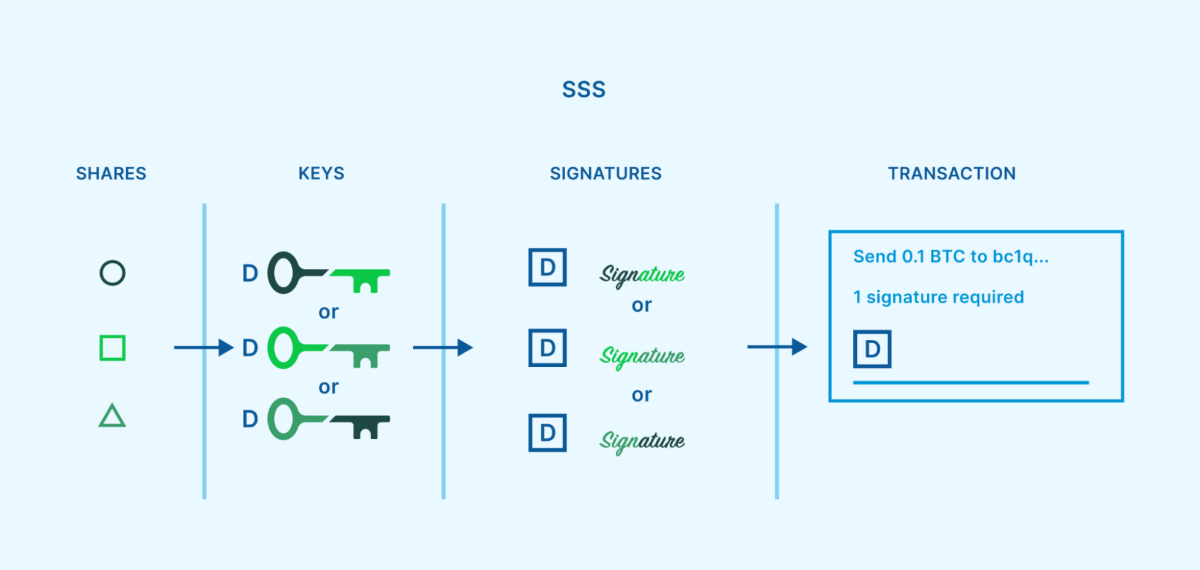
Nevertheless, this method nonetheless results in single factors of failure at sure situations throughout its lifecycle. One instance is when the secret is initially break up up into SSS shares. This operation is normally achieved on a single gadget at a single time and place. If an attacker compromises that gadget, the important thing technology course of or the share creation course of, they’ve compromised the important thing. One other instance is each time the person must reassemble the important thing to signal a transaction. A threshold variety of shares have to be introduced collectively, as soon as once more on a single gadget at a single time and place, which an attacker may exploit.
A reasonably easy and broadly used technique of implementing SSS expertise for cryptocurrency custody is thru the Shamir backup, developed by Satoshi Labs in 2017. It may be discovered as an possibility in sure Trezor {hardware} pockets fashions.

What’s MPC?
MPC, or multi-party computation, is a subfield of cryptography that traces again to the Seventies. The objective of MPC is to permit a number of individuals to collectively carry out a computation, whereas every participant’s contribution to the computation shouldn’t be revealed to the remainder of the group and subsequently can stay non-public. This permits for a number of events to collaborate in varied contexts with no need to belief one another.
When utilized to bitcoin custody, MPC includes distributed “shares,” much like SSS. Nevertheless, not like SSS, the shares aren’t break up from a non-public key nor used to rebuild a non-public key. As an alternative, a number of events compute a single signature instantly from a threshold of their shares.
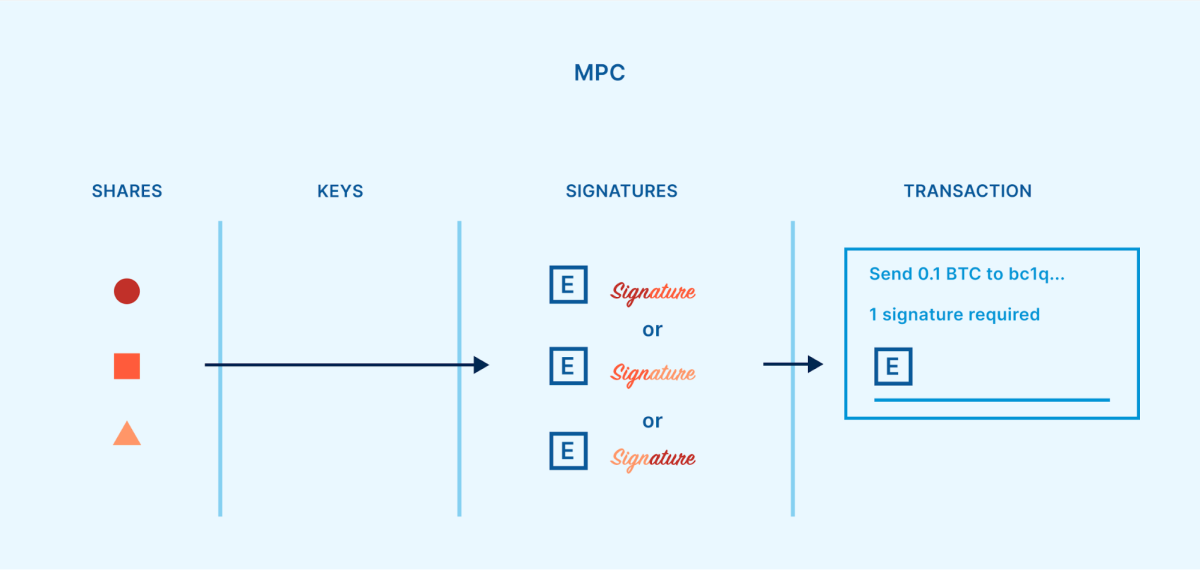
Not like SSS, MPC doesn’t necessitate a single level of failure. MPC shares could be generated individually from each other, they usually by no means must be introduced collectively to function the pockets. Info produced from a share could be communicated to the opposite individuals, with out the share itself being revealed.
Since bitcoin and different cryptocurrencies have primarily used a signature system based mostly on ECDSA (Elliptic Curve Digital Signature Algorithm), MPC needed to be tailored for this context. The primary sensible threshold protocols for ECDSA have been printed in 2018. [GG18, LNR18]
What are the trade-offs between threshold fashions?
With three completely different threshold safety fashions to select from, the following step is knowing the strengths and weaknesses of every possibility.
Tradeoffs with multisig
Script multisig is a standardized method of reaching threshold safety, native to the bitcoin protocol. The construction is taken into account comparatively easy and sturdy. The barrier to entry can be small—if a bitcoin person is aware of learn how to function a singlesig pockets, then it’s not a big leap to discover ways to arrange and use a multisig pockets.
When a multisig pockets is initialized, the addresses produced for receiving bitcoin into the pockets have the brink requirement constructed into them. As soon as a multisig tackle has been funded, the bitcoin is protected by an immutable contract that has primarily been written into the blockchain itself. The one strategy to alter the contract (corresponding to altering the entry management coverage, adjusting which keys are defending the bitcoin) is to maneuver the bitcoin to a brand new tackle that was constructed with a unique contract. For a number of events who’re collaborating to safe bitcoin, this ground-level immutable contract mechanism can present the best diploma of reassurance that the cash is secured based on how all events have supposed. If something have been to be basically modified, it will turn into apparent to everybody by the prevalence of a public transaction, and the keys that accepted the change can be recognized. This is the reason collaborative custody suppliers corresponding to Unchained depend on script multisig for our merchandise.
Nevertheless, deploying contracts publicly on the blockchain comes with tradeoffs. As bitcoin is spent out of a multisig tackle, the entry management coverage for that tackle have to be completely printed on the blockchain. Observers can then see the main points of the multisig quorum that was getting used. Though the remaining funds could be simply migrated to a brand new tackle going ahead, the truth that previous safety preparations are uncovered isn’t supreme. Moreover, needing to maneuver bitcoin from one tackle to a different with a purpose to alter the entry management coverage implies that transaction charges are at all times concerned with the method (and the bigger the quorum, the dearer will probably be).
For entities that worth custodying altcoins, corresponding to cryptocurrency exchanges, script multisig can pose extra of a problem than the opposite two strategies of threshold safety. It’s because a multisig threshold quorum is imposed on the blockchain degree, and completely different cryptocurrencies use completely different blockchains. Many cryptocurrencies don’t even help a local, sturdy multisig implementation in any respect. In the meantime, SSS and MPC implement threshold quorums on the key degree, and seem like singlesig transactions publicly. Since nearly all cryptocurrencies help the same customary for singlesig custody (the identical key can be utilized throughout most cryptocurrencies), this enables SSS and MPC to be extra cross-chain suitable.
Tradeoffs with Shamir’s secret sharing
SSS gives one other method of designing a threshold requirement based mostly on comparatively easy and battle-tested cryptography. For the needs of cryptocurrency custody, SSS additionally has a broadly deployed technique with a low barrier to entry (Shamir backup). As soon as somebody has expertise utilizing a traditional singlesig pockets, it isn’t an enormous leap to make use of a Trezor to arrange a pockets with a Shamir backup.
Not like multisig, SSS operates fully outdoors of public-facing addresses and transactions on the blockchain. As an alternative, the brink requirement is set by how the non-public secret’s break up into shares. Which means that splitting a key into shares and later reassembling them could be achieved in non-public, in order that solely the individuals collaborating within the bitcoin custody association are conscious that SSS is getting used. Along with privateness benefits, preserving the brink construction outdoors of the blockchain additionally implies that SSS transactions gained’t result in elevated charges, and it may be used to safe many alternative cryptocurrencies. Though most cryptocurrencies have their very own distinctive blockchains, they will all share the identical non-public key as an entry level, and that key can in flip be break up up utilizing SSS.
The most important drawback to SSS has already been talked about above—the non-public key should exist in a single place at one time, earlier than it’s first break up into shares, and likewise when the shares are recombined for the needs of approving a withdrawal. These vulnerabilities create short-term single factors of failure, that means that SSS by itself doesn’t provide actually institutional-grade safety, not like multisig or MPC.
Moreover, SSS doesn’t natively provide a technique for adjusting the entry management coverage. As soon as a non-public secret’s break up right into a quorum of shares, these shares will at all times preserve the flexibility to breed that key. If a gaggle is securing a treasury collectively utilizing SSS and a member of the group leaves, revoking permissions for that particular person in a safe method can pose a problem. Remaining members of the group may reassemble the important thing after which break up it into new shares, however the outdated shares would must be verifiably destroyed. In any other case, the funds would must be despatched to a completely new pockets protected by a unique key.
Tradeoffs with MPC
Very similar to SSS, MPC enforces the brink requirement on the key-level as an alternative of the blockchain-level. This unlocks related benefits, corresponding to granting the next capability for privateness, avoiding elevated transaction charges, and permitting for one MPC custody construction for use throughout many alternative cryptocurrencies.
Importantly, MPC manages to keep away from the short-term single factors of failure that include utilizing SSS. Through the use of a unique cryptographic technique, the important thing shares can exist individually from the second the pockets is first created, and even stay separate whereas signing withdrawal transactions. Most MPC implementations additionally embrace a local technique of adjusting the entry management coverage (creating a brand new quorum of shares) with out having to ship funds to a brand new pockets tackle.
Nevertheless, MPC for threshold ECDSA is taken into account very complicated cryptography, and there’s not an agreed-upon customary for utilizing it. There are various completely different protocols, with the primary two being developed independently in 2018 by Gennaro and Goldfeder [GG18] and Lindell et al. [LNR18]. Since then, we’ve additionally seen protocols from Doerner et al. [DKLs19], Castagnos et al. [CCL+20], Damgård et al. [DJM+20], Canetti et al. [CMP20], Gągol et al. [GKSS20], Gennaro and Goldfeder [GG20], Canetti et al. [CGG+21], Abram et al. [ANO+21], Doerner et al. [DKLs23], and maybe others. Whereas the newer protocols are inclined to make sure enhancements upon the older ones, they could have had much less alternative for peer-review, audit, and different testing.
The upper degree of complexity concerned with MPC creates a widened assault floor. With extra elements and procedures, there’s extra room for error and potential safety vulnerabilities. Proof of great safety flaws, together with full non-public key extraction assaults, has already offered itself greater than as soon as, affecting among the threshold ECDSA protocols listed above.
Examples embrace:
AS20 vulnerabilities, September 2020, affecting GG18 implementations
Alpha-Rays vulnerabilities, December 2021, affecting GG18 and GG20
TSSHOCK vulnerabilities, August 2023, affecting GG18, GG20, and CGG+21
BitForge vulnerabilities, August 2023, affecting GG18 and GG20
“Cryptography must move the check of time to achieve longevity, and these new protocols clearly didn’t move the check of time[…] this analysis was not prepared for implementation or widespread adoption. From my perspective, implementing and productizing such current analysis is kind of harmful.” — Ledger CTO Charles Guillemet, December 2021 response to Alpha-Rays
“[MPC is] extra sophisticated, extra to get flawed. Superior crypto protocols are fragile within the element and within the implementation. I might really feel extra assured in multisig, which is tremendous easy and rock strong.” — Publish by famend cryptographer Adam Again, January 2023
MPC can be restricted by who can realistically use it within the first place. As beforehand talked about, threshold ECDSA could be very sophisticated. For the typical particular person, there aren’t any instruments accessible to soundly or simply arrange MPC independently. Whereas some companies provide collaborative custody MPC wallets which are pretty simple to make use of, these companies provide no simple method for customers to get well funds if the enterprise disappears (or no method in any respect, wherein case they’re a single level of failure). As a result of script multisig is a straightforward and open customary, companies who present collaborative custody options utilizing multisig can provide open-source and easy-to-use restoration instruments. This creates an easy avenue for purchasers to get well their funds even when the collaborative multisig enterprise have been not accessible to help.
Which mannequin is finest?
As we simply coated, there are quite a few tradeoffs between utilizing multisig, SSS, and MPC. They are often organized in a chart for a visible comparability:
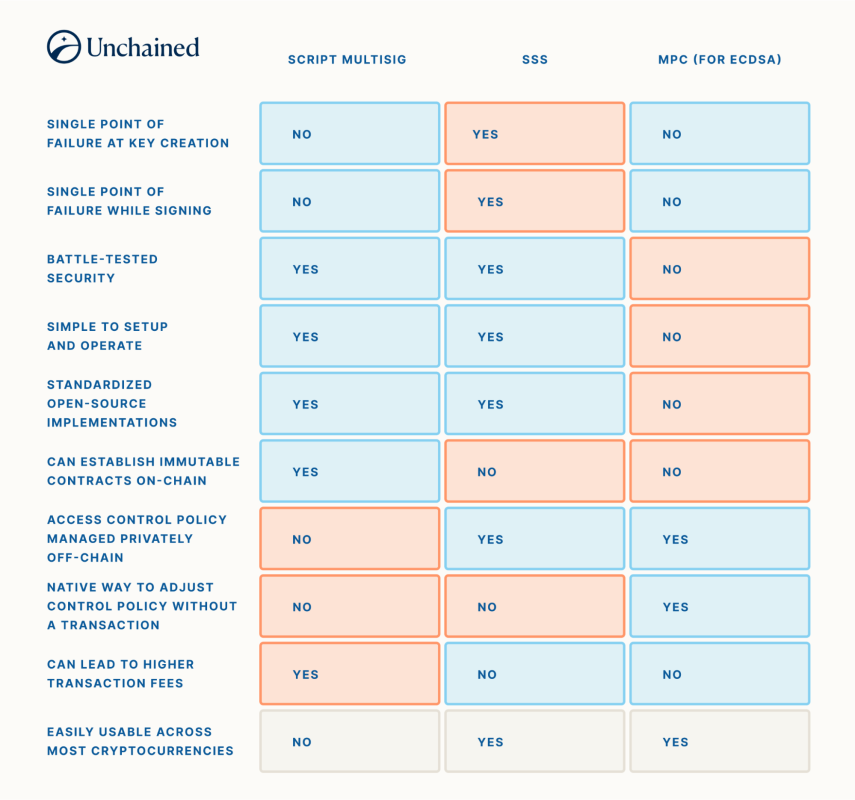
If a enterprise specializes within the custody of many alternative cryptocurrencies, they may be motivated to rent a group of pros to rigorously arrange an MPC custody mannequin. Nevertheless, if a enterprise or particular person have been in search of a easy and dependable strategy to safe bitcoin for the long run, utilizing script multisig and accepting the privateness tradeoffs may be preferable. SSS is never utilized by itself on account of its incapability to implement institutional-grade threshold necessities always.
Combining fashions for collaborative custody
Whereas multisig, SSS, and MPC are sometimes considered competing safety fashions, it’s attainable to include multiple of them into an general custody construction. As beforehand described, SSS and MPC enable a threshold of key shares to supply a signature for a transaction. If the signature was for spending funds out of a singlesig pockets, then nothing else can be required to finish the transaction. Nevertheless, if as an alternative the signature was for spending funds out of a multisig pockets, extra signatures from different keys may be wanted.
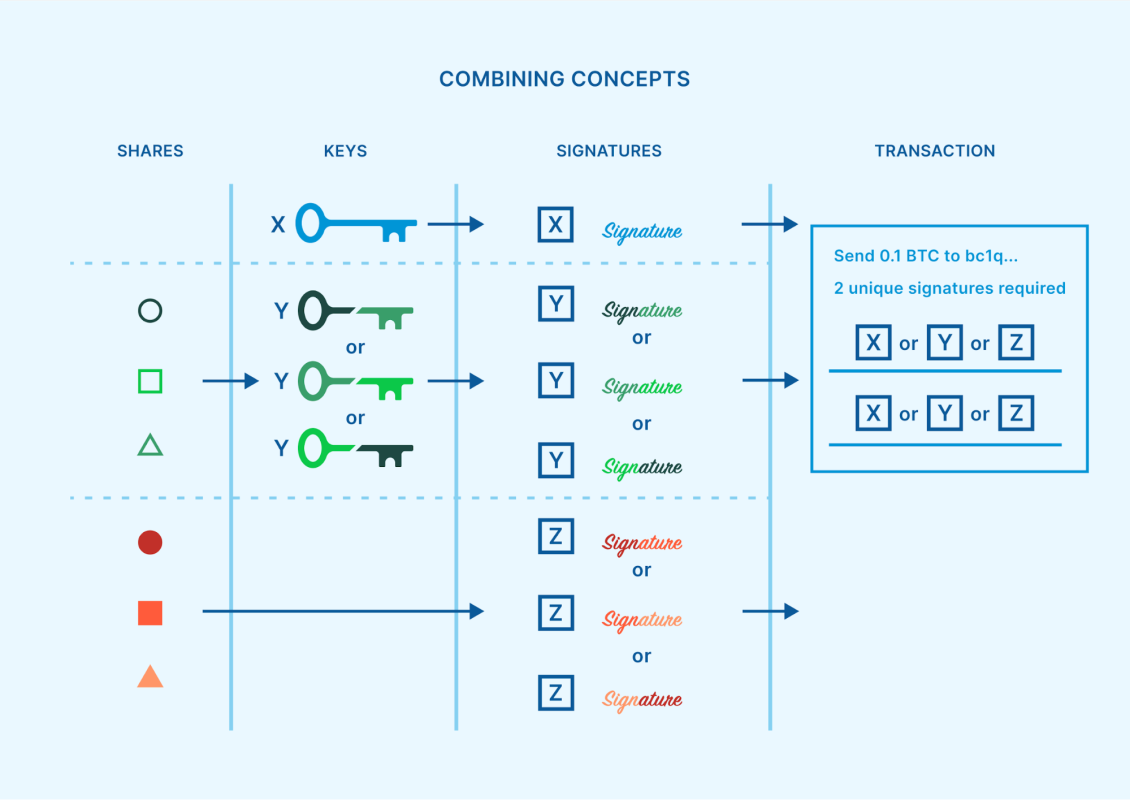
Whereas this mix of strategies might sound pointless and cumbersome, there are certainly some contexts the place it makes sensible sense. With the rise in reputation of key brokers and multi-institution custody, there’s a rising variety of specialty companies which are commissioned by people and establishments to safe one of many keys to a multisig pockets. These distributed key brokers may help cut back custodial danger. However how ought to a key agent safe that single key which they’re chargeable for?
SSS or MPC could be a technique to attenuate or take away single factors of failure from this responsibility. A company key agent can design a system the place a number of completely different officers throughout the enterprise every maintain key shares, and subsequently a signature can solely be produced upon settlement from a threshold of these officers. Moreover, if an assault have been to happen throughout an SSS reassembly, or an MPC implementation finally ends up affected by a brand new key extraction vulnerability like those listed earlier, then no buyer funds are instantly in danger. The important thing agent would have time to react and tackle the problem, whereas the bitcoin stays protected by the broader multisig pockets.
Utilizing script multisig to create a threshold requirement as a foundational immutable contract, after which commissioning skilled key brokers to every defend a multisig key utilizing their very own SSS or MPC threshold, is much and away the most secure technique for an establishment to maintain bitcoin secured for the long-term.
New capabilities with Taproot
In November of 2021, the Taproot soft-fork occurred, including new instruments into the bitcoin ecosystem. A few of these instruments influence the way forward for institutional-grade bitcoin custody, by permitting for sure enhancements and optionalities.
Schnorr signatures: The Schnorr signature algorithm is now accessible in bitcoin as a substitute for ECDSA. Utilizing MPC on prime of Schnorr results in threshold safety schemes which are far simpler, and subsequently additionally present larger confidence of their safety, in comparison with the ECDSA protocols talked about earlier. FROST is the main Schnorr threshold signature protocol, whereas MuSig2 can be accessible particularly for N-of-N quorums. Each of those signature schemes are on the trail to changing into standardized instruments throughout the bitcoin business, and they’re anticipated to make MPC accessible for normal people, with a person expertise much like script multisig.Script sort privateness: Pay-to-Taproot (P2TR) addresses are a brand new tackle sort that enable script multisig bitcoin addresses to seem an identical to the addresses getting used for singlesig wallets. This offers a major privateness enchancment, as a result of it implies that the bitcoin tackle itself doesn’t present any clues about its proprietor’s safety mannequin, corresponding to whether or not or not they may be utilizing script multisig.A number of spending paths: P2TR addresses even have the flexibility to comprise a number of spending paths constructed into them. This could create new methods of structuring threshold safety for institutional-grade custody, as described in BIP 342 (rationale, part 5). For instance, a person may create an N-of-N script multisig spending path for each mixture of keys that may spend funds. Relatively than construct a 2-of-3 quorum with keys A, B, and C, the same consequence could be achieved with three separate 2-of-2 quorums as attainable spending paths—one with keys A and B, one with keys A and C, and one with keys B and C. This technique can improve privateness, as a result of solely the spending path that finally ends up getting used might be revealed. An analogous idea could be utilized to MPC key share quorums, permitting MuSig2 to be utilized for thresholds.
These Taproot instruments are comparatively new, and their adoption continues to be within the early phases. Many bitcoin softwares and companies don’t but provide full help for what Taproot has to supply. It’s additionally price noting that the majority altcoins don’t have these instruments natively accessible.
Ultimate ideas
A rising variety of establishments have gotten concerned about securing a bitcoin treasury, they usually require efficient options. Avoiding single factors of failure and minimizing counterparty danger are paramount concerns. One of the best ways to satisfy these standards is by leveraging a multisig construction, the place keys could be distributed amongst varied enterprise key brokers, none of whom could have unilateral management over the bitcoin. Every key agent can use SSS or MPC so as to add further threshold safety for his or her explicit key.
Unchained has pioneered an enterprise custody community, constructed for institutional purchasers who wish to arrange an association like this. It’s simple to make use of and customizable, so that every shopper will get to decide on whether or not they’d like to carry a controlling variety of keys themselves, or only a single key, or go away the duty of securing keys completely as much as the a number of, unbiased enterprise key brokers. In the event you’re concerned about studying extra, schedule a free session with us at the moment!
Particular due to Dhruv Bansal for reviewing this text and offering priceless suggestions.
Initially printed on Unchained.com.
Unchained Capital is the official US Collaborative Custody associate of Bitcoin Journal and an integral sponsor of associated content material printed by Bitcoin Journal. For extra info on companies supplied, custody merchandise, and the connection between Unchained and Bitcoin Journal, please go to our web site.









