Final week, the federal government of Brazil banned X, previously Twitter, chopping off hundreds of thousands of customers from the Elon Musk-owned social community. It is among the extra high-profile examples of restrictions positioned on platforms, and disputes world wide span a large number of causes: free speech (a minimum of within the U.S.), political dissent, copyright, and criminal activity.
Whereas alternate social media platforms like Bluesky noticed a surge in new customers from Brazil after the ban, some nonetheless insistent on utilizing X have turned to digital non-public networks (VPNs)—although doing so can also be forbidden by the Brazilian authorities, and violations may include a hefty every day fantastic.
Different subtle instruments for obfuscating your location embody the Tor Browser.
Not all VPNs are created equal. Decrypt spoke to the chief director of Unredacted Inc., a 501(c)(3) non-profit group that gives free and open providers that assist folks evade censorship and shield their proper to privateness.
What’s a VPN?
IP addresses—numbers assigned to each community on the web—are like a digital fingerprint. They reveal a substantial quantity of data, together with bodily location, what web supplier you employ, and so forth. They’re usually the way in which entry is “geofenced” or restricted to or from particular areas or jurisdictions.
VPNs obscure this data in addition to encrypt connections to stop snooping by third events.
“For instance, in case you are in Brazil and X is blocked, you need to use a VPN to tunnel packets destined for X within a VPN tunnel to a different nation,” Zach, the chief director of Unredacted Inc., advised Decrypt. (He requested that his final identify not be used.) “An ISP or authorities couldn’t examine what’s inside that tunneled site visitors with out the encryption keys out of your VPN supplier or machine.”
A mega thread about how Brazilians (& others) can circumvent the censorship of X, and any subsequent makes an attempt to censor different providers & platforms 🧵👇
There are a number of choices at your disposal, however first we wish to make it clear that it is not significantly secure to make use of a uncooked VPN…
— Unredacted (@unredacted_org) September 1, 2024
The issue, Zach stated, is that many VPNs don’t attempt to disguise the truth that they’re VPNs.
“Frequent VPN protocols similar to OpenVPN or WireGuard can simply be fingerprinted primarily based on widespread port numbers or by way of DPI (deep packet inspection) by a authorities or ISP,” Zach stated. “Using typical VPN protocols is not any secret to your ISP and authorities, and in some conditions, it may endanger the person.”
As Zach defined, it is also widespread for VPN suppliers to get pressured by authorities entities to share person knowledge in an effort to examine criminals and terrorist teams who could also be making an attempt to cover their actions utilizing a VPN.
“Folks can use VPNs for malicious functions, as is true with any software,” Zach stated. “Governments will usually ship subpoenas attempting to find the true origin of VPN site visitors and request subscriber particulars for a particular timestamp the place an offense occurred.”
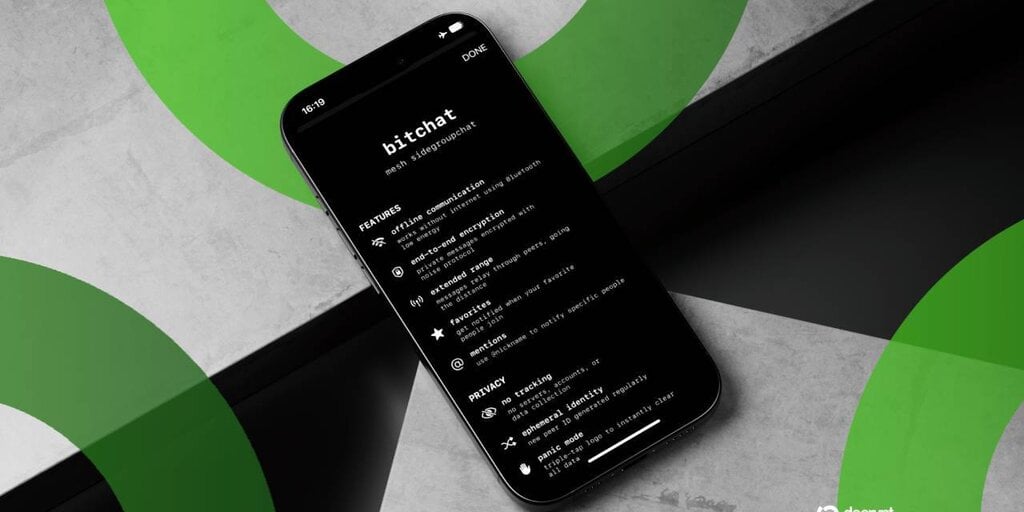
As a substitute of utilizing a “uncooked VPN,” Unredacted factors folks to “obfuscated protocols.”
Zach famous that protocols like Shadowsocks—which is utilized by Define VPN—and Tor transports like webtunnel, snowflake, meek, and obfs4 are more durable to fingerprint than conventional VPNs, making them safer options.
VPNs should not a silver bullet
Zach cautioned that every one site visitors might be fingerprinted if it shares observable patterns, nonetheless. Extra superior authorities censorship operations usually attempt to block VPN protocols, however doing so could cause collateral injury, like disrupting reliable web sites and communication platforms.
“These requests are typically made with good intentions,” he acknowledged. “What’s worrying is broad requests for extra knowledge than is really obligatory.”
The much less knowledge collected by a VPN supplier, the higher. Zach really useful that when selecting a VPN, one search for verifiable no-logging claims and overview the supplier’s safety coverage and privateness stance. Test to see if they’re open-source and have undergone third-party audits, he added.
“Many VPN suppliers use online marketing and social media to advertise their service, however it’s essential to analysis their claims and search for how they’ve dealt with previous requests for knowledge,” he stated. “In a technical sense, it’s potential for any supplier to activate logging at any time with out your information.”
Non-public choices
Well-liked VPNs embody NordVPN, ProtonVPN, SurfShark, and ExpressVPN. There are additionally decentralized VPN (DPN) choices from firms like Mysterium Community, Orchid, Deeper Community, and Tachyon.
Past these fundamentals?
“There are numerous nice choices—for much less technical folks, Tor Browser and Tor’s Orbot (which acts like a conventional VPN) are very simple to make use of and perceive,” Zach stated. “Define VPN is one other pretty simple possibility to know, with easy-to-use cross-platform apps.
“Our service, FreeSocks, helps folks in closely censored nations hook up with the Define servers at no cost that we function,” he added.
Zach defined that each Tor and Define assist circumvent censorship in lots of nations worldwide.
“It is essential to level out that utilizing Tor Browser or Orbot is inherently one of many most secure strategies to bypass censorship and shield a person’s privateness due to the very fact it hops your connection by three randomized nodes when accessing the common Web by it,” he stated. “This makes correlation assaults very troublesome.”
Typically Clever Publication
A weekly AI journey narrated by Gen, a generative AI mannequin.