On-chain safety researcher ZachXBT flagged a whole bunch of wallets throughout a number of EVM chains getting drained for small quantities, sometimes below $2,000 per sufferer, funneling right into a single suspicious handle.
The theft whole climbed previous $107,000 and stored rising. The foundation trigger continues to be unknown, however customers reported receiving a phishing e mail disguised as a compulsory MetaMask improve, full with a party-hat fox emblem and a “Completely satisfied New 12 months!” topic line.
This assault arrived when builders had been on vacation, assist channels had been operating skeleton crews, and customers had been scrolling by way of inboxes cluttered with New 12 months promotions.
Attackers exploit that window. The small per-victim quantities recommend the drainer operates off contract approvals relatively than full seed-phrase compromise in lots of instances, which retains particular person losses beneath the edge the place victims instantly sound alarms however permits the attacker to scale throughout a whole bunch of wallets.
The business continues to be processing a separate Belief Pockets browser extension incident during which malicious code in Chrome extension v2.68 harvested personal keys and drained no less than $8.5 million from 2,520 wallets earlier than Belief Pockets patched to v2.69.
Two totally different exploits, similar lesson: person endpoints stay the weakest hyperlink.
Anatomy of a phishing e mail that works
The MetaMask-themed phishing e mail demonstrates why these assaults succeed.
The sender id exhibits “MetaLiveChain,” a reputation that sounds vaguely DeFi-adjacent however has no connection to MetaMask.
The e-mail header comprises an unsubscribe hyperlink for “[email protected],” revealing that the attacker lifted templates from official advertising campaigns. The physique options MetaMask’s fox emblem sporting a celebration hat, mixing seasonal cheer with manufactured urgency a few “necessary replace.”
That mixture bypasses the heuristics most customers apply to apparent scams.
MetaMask’s official safety documentation establishes clear guidelines. Assist emails come solely from verified addresses, equivalent to [email protected], and by no means from third-party domains.
The pockets supplier doesn’t ship unsolicited emails demanding verification or upgrades.
Moreover, no consultant will ever ask for a Secret Restoration Phrase. But these emails work as a result of they exploit the hole between what customers know intellectually and what they do reflexively when an official-looking message arrives.
4 alerts expose phishing earlier than injury happens.
First, brand-sender mismatch, as MetaMask branding from “MetaLiveChain” alerts template theft. Second, manufactured urgency round necessary updates that MetaMask explicitly says it is not going to ship.
Third, vacation spot URLs that do not match claimed domains, hovering earlier than clicking reveals the precise goal. Fourth, requests that violate core pockets guidelines, equivalent to asking for seed phrases or prompting for signatures on opaque off-chain messages.
The ZachXBT case demonstrates signature-phishing mechanics. Victims who clicked the pretend improve hyperlink seemingly signed a contract approval granting the drainer permission to maneuver tokens.
That single signature opened the door to ongoing theft throughout a number of chains. The attacker selected small per-wallet quantities as a result of contract approvals usually carry limitless spend caps by default, however draining every thing would set off quick investigations.
Spreading theft throughout a whole bunch of victims at $2,000 every flies below the person radar whereas accumulating six-figure totals.
Revoking approvals and shrinking blast radius
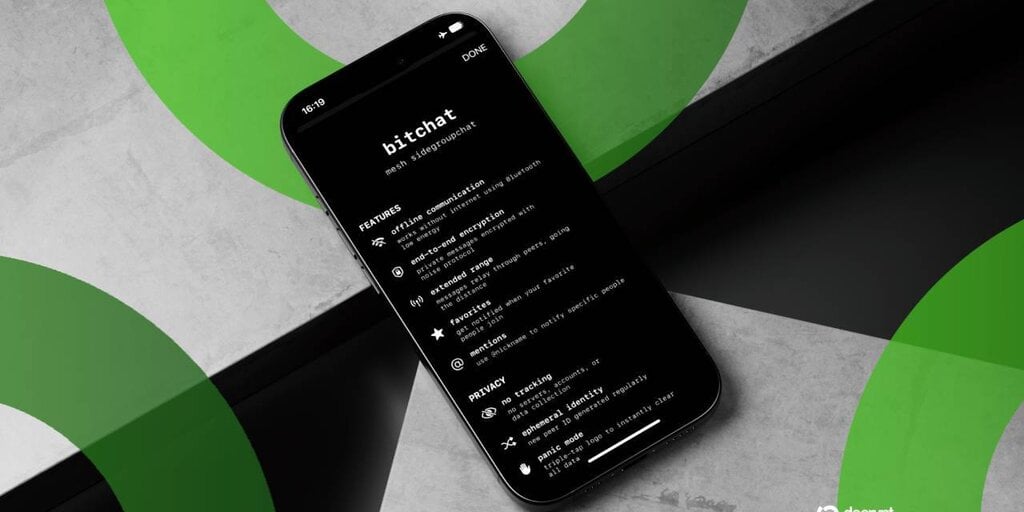
As soon as a phishing hyperlink is clicked or a malicious approval is signed, precedence shifts to containment. MetaMask now lets customers view and revoke token allowances instantly inside MetaMask Portfolio.
Revoke.money walks customers by way of a easy course of: join your pockets, examine approvals per community, and ship revoke transactions for untrusted contracts.
Etherscan’s Token Approvals web page gives the identical performance for handbook revocation of ERC-20, ERC-721, and ERC-1155 approvals. These instruments matter as a result of victims who act quick might lower off the drainer’s entry earlier than dropping every thing.
The excellence between approval compromise and seed-phrase compromise determines whether or not a pockets might be salvaged. MetaMask’s safety information attracts a tough line: in case you suspect your Secret Restoration Phrase has been uncovered, cease utilizing that pockets instantly.
Create a brand new pockets on a contemporary system, switch remaining property, and deal with the unique seed as completely burned. Revoking approvals helps when the attacker solely holds contract permissions; in case your seed is gone, your complete pockets should be deserted.
Chainalysis documented roughly 158,000 private pockets compromises affecting no less than 80,000 folks in 2025, whilst whole stolen worth fell to roughly $713 million.

Attackers hit extra wallets for smaller quantities, the sample ZachXBT recognized. The sensible implication: organizing wallets to restrict blast radius issues as a lot as avoiding phishing.
A single compromised pockets shouldn’t imply whole portfolio loss.
Constructing defense-in-depth
Pockets suppliers have shipped options that might have contained this assault if adopted.
MetaMask now encourages setting spending caps on token approvals relatively than accepting the default “limitless” permissions. Revoke.money and De.Fi’s Protect dashboard advocate treats approval evaluations as routine hygiene alongside {hardware} pockets use for long-term holdings.
MetaMask permits transaction safety alerts from Blockaid by default, flagging suspicious contracts earlier than signatures are executed.
The Belief Pockets extension incident reinforces the necessity for defense-in-depth. That exploit bypassed person choices, and malicious code in an official Chrome itemizing mechanically harvested keys.
Customers who segregated holdings throughout {hardware} wallets (chilly storage), software program wallets (heat transactions), and burner wallets (experimental protocols) restricted publicity.
That three-tier mannequin creates friction, however friction is the purpose. A phishing e mail that captures a burner pockets prices a whole bunch or just a few thousand {dollars}. The identical assault in opposition to a single pockets holding a whole portfolio prices life-changing cash.
The ZachXBT drainer succeeded as a result of it focused the seam between comfort and safety. Most customers hold every thing in a single MetaMask occasion as a result of managing a number of wallets feels cumbersome.
The attacker guess {that a} professional-looking e mail on New 12 months’s Day would catch sufficient folks off guard to generate worthwhile quantity. That guess paid off, with $107,000 and counting.

What’s at stake
This incident poses a deeper query: who bears accountability for endpoint safety in a self-custodial world?
Pockets suppliers construct anti-phishing instruments, researchers publish risk reviews, and regulators warn shoppers. But the attacker wanted solely a pretend e mail, a cloned emblem, and a drainer contract to compromise a whole bunch of wallets.
The infrastructure that allows self-custody, permissionless transactions, pseudonymous addresses, and irreversible transfers additionally makes it unforgiving.
The business treats this as an schooling downside: if customers verified sender addresses, hover over hyperlinks, and revoke previous approvals, assaults would fail.
But, Chainalysis’s information on 158,000 compromises suggests schooling alone does not scale. Attackers adapt sooner than customers be taught. The MetaMask phishing e mail developed from crude “Your pockets is locked!” templates to polished seasonal campaigns.
The Belief Pockets extension exploit proved that even cautious customers can lose funds if distribution channels get compromised.
What works: {hardware} wallets for significant holdings, ruthless approval revocation, pockets segregation by danger profile, and skepticism towards any unsolicited message from pockets suppliers.
What does not work: assuming pockets interfaces are secure by default, treating approvals as one-time choices, or consolidating all property in a single scorching pockets for comfort. The ZachXBT drainer will likely be shut down as a result of the handle is flagged, and exchanges will freeze deposits.
However one other drainer will launch subsequent week with a barely totally different template and a brand new contractaddress.
The cycle continues till customers internalize that the comfort of crypto creates an assault floor that finally will get exploited. The selection is not between safety and usefulness, however considerably between friction now and loss later.