Briefly
Treasury sanctions alleged Sergey Sergeyevich Zelenyuk and Operation Zero operated as a Russian exploit dealer community.
Based on Regulators, the sanctions are the primary actions below the brand new commerce secrets and techniques sanctions regulation.
The stolen “instruments” had been constructed for unique U.S. authorities use.
The U.S. Treasury Division on Tuesday stated it has sanctioned a Russian dealer dealing in exploits, accused of promoting stolen U.S. authorities cyber instruments.
The sanctions focused Sergey Sergeyevich Zelenyuk and his St. Petersburg-based agency, Matrix LLC, also referred to as “Operation Zero.”
The sanctions mark the primary use of the Defending American Mental Property Act to deal with the theft and sale of digital commerce secrets and techniques, in response to the Workplace of International Belongings Management.
]]>
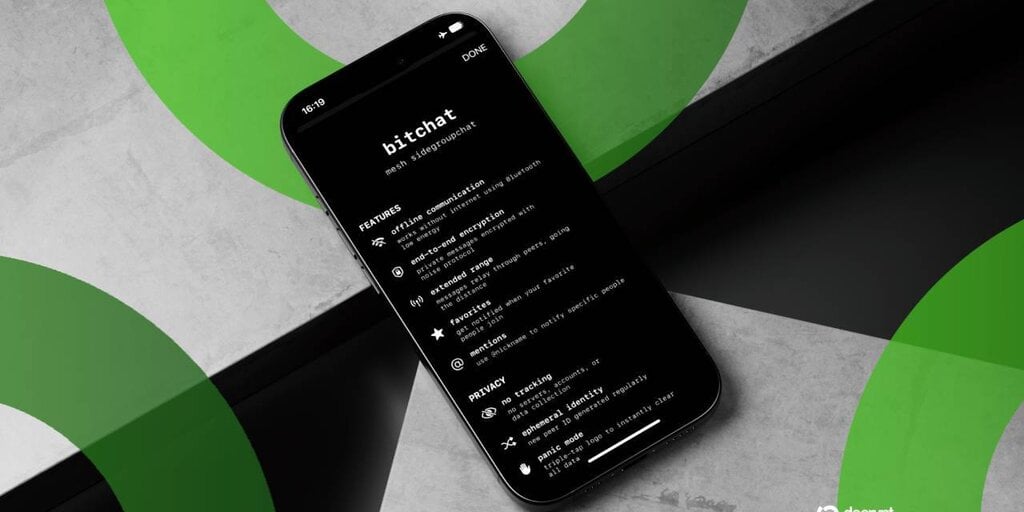
“Zelenyuk and Operation Zero commerce in ‘exploits,’ items of code or methods that make the most of vulnerabilities in a pc program to permit customers to realize unauthorized entry, steal info, or take management of an digital system,” OFAC stated in an announcement on Tuesday.
Operation Zero would then supply bounties to anybody who supplied exploits for U.S.-built software program, OFAC added.
Treasury additionally sanctioned Oleg Vyacheslavovich Kucherov, a suspected member of the Trickbot cybercrime gang, and Marina Evgenyevna Vasanovich, described as Zelenyuk’s assistant.
Launched in 2021, Operation Zero has supplied multimillion-dollar bounties for vulnerabilities in working methods and encrypted messaging purposes.
Operation Zero didn’t conceal its bounties, lots of which had been brazenly printed on X. One bounty put up in November supplied as much as $500,000 for an exploit concentrating on Apple’s iOS 26. A bounty from March 2025 supplied as much as $4 million for Telegram “full chain” exploits.
Operation Zero’s shoppers are “Russian non-public and authorities organizations solely,” for these searching for to buy “analysis, merchandise, and software program code within the discipline of offensive safety,” in response to a tough translation of the corporate’s web site.
“Zero-day acquisition is a well-liked and customary observe in lots of nations these days,” the corporate stated in its FAQ. “It’s not solely far more profitable than working with bug bounties and distributors however extra protected as effectively,” including {that a} researcher who works with Operation Zero shouldn’t should commerce privateness and security for cash.
Operation Zero has stolen not less than eight proprietary “cyber instruments” developed for the unique use of the U.S. authorities and choose allies, in response to the Treasury Division.
The U.S. State Division stated Tuesday in a separate assertion that the motion follows a Justice Division and FBI investigation into Peter Williams, an Australian nationwide and former worker of a U.S. protection contractor, who allegedly stole “eight commerce secret zero-day exploits” from 2022 by to 2025.
“These elements had been meant to be offered solely to the U.S. authorities and choose allies, the state division stated. “He offered these exploits to Operation Zero in change for $1.3 million in crypto funds.” Williams pleaded responsible in October of final yr to 2 counts of theft of commerce secrets and techniques.
Treasury stated the Russian firm has additionally labored to develop spyware and adware and AI-based instruments to extract private figuring out info and different delicate knowledge. It has additionally used social media to recruit hackers and construct relationships with international intelligence companies.
The Treasury Division and Operation Zero didn’t instantly reply to Decrypt’s requests for remark.
Each day Debrief E-newsletter
Begin every single day with the highest information tales proper now, plus unique options, a podcast, movies and extra.