The info sitting inside a compliance archive is a number of the most delicate of any group. Monetary data, regulated communications, and personally identifiable data are all collected and reside inside it.
But when corporations select a compliance vendor, the dialog typically solely asks: does it seize the fitting channels, meet the related laws, and combine cleanly with current infrastructure?
What that course of virtually by no means contains is a direct query in regards to the safety posture of the seller. A part of the reason being structural. Compliance officers concentrate on whether or not the platform meets regulatory necessities, and IT and safety groups consider infrastructure match. The opposite purpose is as a result of most groups function on the belief that compliance means safe.
However these are two totally completely different mandates. “Compliance is about assembly regulatory record-keeping guidelines like FINRA, GDPR, POPIA, and MiFID II,” says Simon Peters, Director of Channel Gross sales at Smarsh. “Safety is proactive safety towards breaches, insider threats, and unauthorized entry to all knowledge.”
Combining them is exactly the place organizations turn out to be uncovered.
Associated Tales
When “Compliant” Isn’t Sufficient: The Hidden Breach Danger
A compliance platform is simply compliant when its integrity is maintained. As soon as it’s breached, the results lengthen far past the seller. The group that entrusted that platform with its most delicate communications now faces a failure of a distinct compliance obligation totally: knowledge safety. Peters explains,
“It may be the provider who was breached, however successfully, it’s the corporate’s breach.”
That reframes vendor choice as a threat administration choice, not only a procurement one.
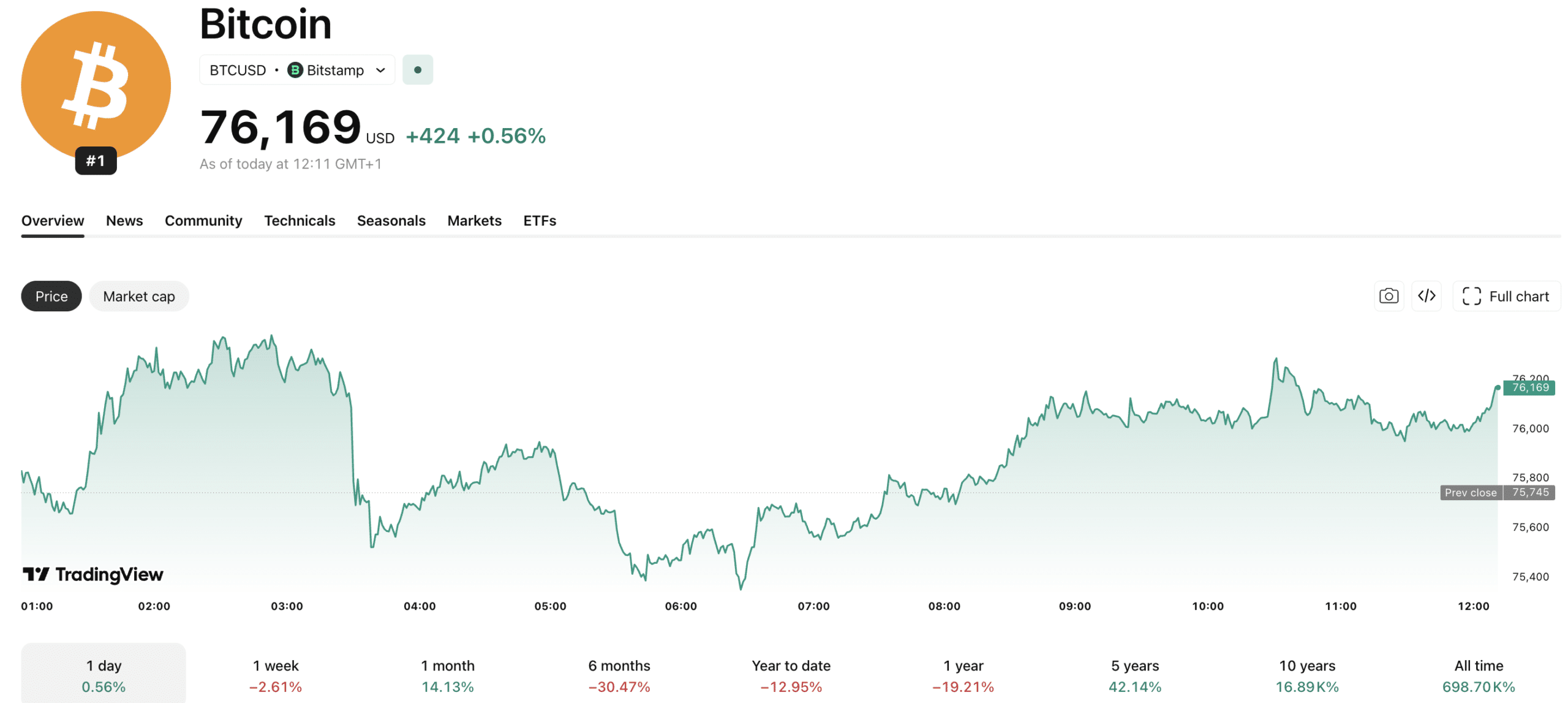
Enforcement makes that threat concrete. The SEC issued a $63 million penalty for knowledge publicity in 2025, and multi-million-dollar fines for PII, PCI, and PHI violations underneath GDPR, POPIA, and HIPAA are now routine. Past monetary publicity, a breach triggers necessary buyer notifications, potential class actions, and reputational injury.
For compliance officers, a vendor breach triggers the very obligations they have been employed to forestall. For IT and safety leaders, it exposes a spot that no incident response plan can simply shut. The archive they assumed was protected turns into the only greatest legal responsibility within the group.
What raises the stakes additional is the character of what compliance archives comprise. Years of regulated conversations, voice recordings, monetary disclosures, and personally identifiable data concentrated in a single place make that archive enticing to attackers, that means will probably be examined always. Legacy instruments constructed primarily round retention have been by no means designed to defend towards that stage of publicity.
How Smarsh Builds Safety In, Not On
Most compliance platforms are constructed to satisfy regulatory necessities first, with safety added later. That sequencing is strictly the issue. Smarsh begins from a distinct premise. Peters explains,
“Safety is constructed into the core of our platform. It’s not a bolt-on.”
Concretely, that enables the platform to ship greater ranges of information safety from the second knowledge enters the platform, versus after it’s settled there. Army-grade 256-bit AES rotating encryption is utilized at seize, maintained by way of transit, and locked at relaxation.
Equally, most platforms share knowledge throughout all clients on the identical infrastructure. Smarsh holds it independently. On high of that, clients management precisely which Azure area their knowledge and AI processing reside in, specifiable right down to the enterprise unit or knowledge kind. Nothing crosses borders. Redaction is automated and in-region.
Entry controls add an extra layer of defensibility. Smarsh applies a zero-trust safety design, granular role-based permissions, full audit logs, IP whitelisting, and timestamp data. Each interplay with archived knowledge is traceable, wealthy with metadata, and tamper-evident, constructed to resist the form of forensic evaluate a regulatory investigation calls for.
When knowledge wants to maneuver for authorized maintain, regulatory evaluate, or export, it might probably journey by way of encrypted snippets or with full audit documentation connected. For organizations in regulated industries, that’s the distinction between an archive that helps compliance and one which ensures it.
Beginning the Proper Dialog
The excellence between compliance and safety has by no means been extra consequential. Regulatory expectations are rising, enforcement is intensifying, and the amount of delicate communications flowing by way of enterprise platforms continues to develop. Treating a compliance vendor as safe by default is a threat most organizations haven’t totally priced in.
For groups involved their present setup won’t maintain up, Peters recommends beginning with 4 questions: What’s the platform’s encryption power? The place precisely does knowledge reside, and the place does the AI processing it function? Does the platform preserve an entire entry log? What redaction protection exists for delicate content material?
Map these third-party knowledge flows earlier than requesting the rest. Realizing the place knowledge goes and who can entry it’s the baseline for a significant safety analysis and the place to begin for a real dialog with any compliance vendor.
Solely by distinguishing between compliance and safety can organizations really defend their most delicate knowledge. Treating them as the identical threat is a mistake that turns into painfully clear after a breach.
For compliance officers and IT safety leaders who need to shut the hole, use Smarsh’s compliance guidelines to search out out whether or not your present platform is as safe as you assume.